Rotating TDE external key manager password
Changing passwords regularly is a common security practice to enhance the overall security of systems and maintain compliance. When OKV or HSM is used with TDE, changing the password of the External Key Manager (EKM) can result in Delphix workflow failures for datasets that rely on the EKM.
When the password of the EKM is rotated, it is necessary to update the TDE Key Manager Credential in the Delphix engine by following the procedure documented in Adding or Editing the TDE External Key Manager Credential.
Additionally, manual steps must be taken to update the credential in the autologin wallet created or shared with Delphix-managed datasets.
To update the password for OKV endpoint, refer to the Oracle OKV documentation. To update the password for Thales CipherTrust, refer to the Thales CipherTrust documentation.
Example for updating the TDE external key manager password for OKV endpoint
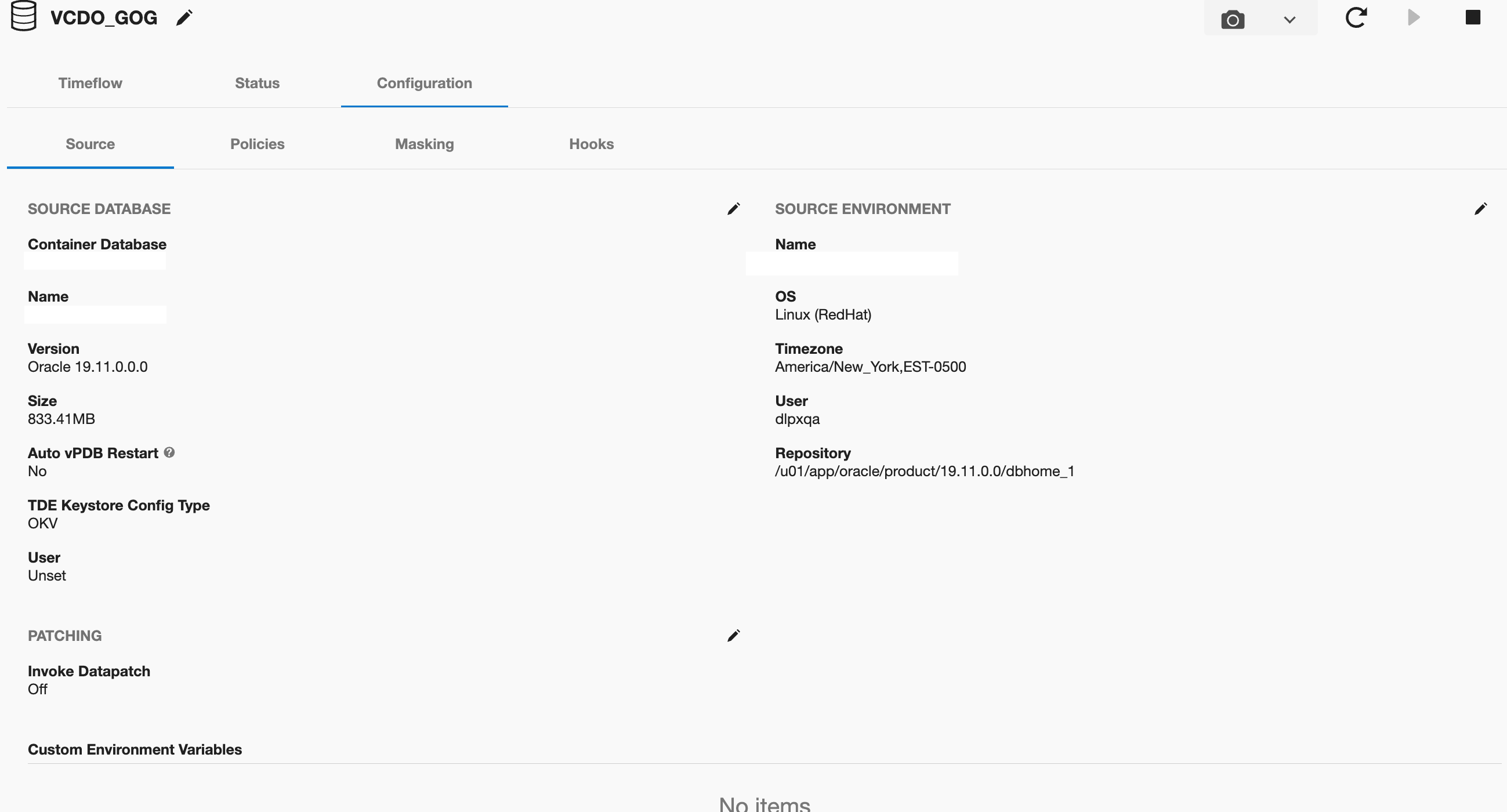
Consider the following TDE OKV-enabled vPDB:
Log in to the database instance CDOMSHTGCF36 as a user who has been granted the
ADMINISTER KEY MANAGEMENTorSYSKMprivilege.Close the external keystore
CODESQL> ADMINISTER KEY MANAGEMENT SET KEYSTORE CLOSE CONTAINER = ALL; keystore altered.Change the Oracle Key Vault endpoint password. The following example shows how to use the okvutil changepwd command to change the endpoint password. When you are prompted to create the new password, enter a password that is between 8 and 30 characters.
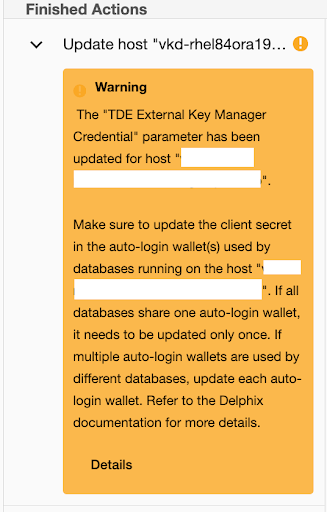
CODE[oracle@ip~]$ $OKV_HOME/bin/okvutil changepwd -l $OKV_HOME/ssl -t WALLET Enter new wallet password: Confirm new wallet password: Wallet password changed successfullyUpdate the TDE Key Manager Credential in Delphix by following the procedure documented in Adding or Editing the TDE External Key Manager Credential. A job warning will be displayed to update the client secret of the autologin wallet.
The old Oracle Key Vault endpoint password was stored in a [local] auto-open wallet within the
WALLET_ROOT/tdedirectory. To update the password, use the following syntax:CODESQL> ADMINISTER KEY MANAGEMENT UPDATE SECRET 'Test@123' FOR CLIENT 'OKV_PASSWORD' TO AUTO_LOGIN KEYSTORE '/work/oracle/tde'; keystore altered.The client secret name for Oracle Key Vault is OKV_PASSWORD, and in the case of a Hardware Security Module, it will be HSM_PASSWORD.
Open the external keystore
CODESQL> ADMINISTER KEY MANAGEMENT SET KEYSTORE OPEN FORCE KEYSTORE IDENTIFIED BY "Test@123" CONTAINER =ALL; keystore altered.
The above steps are also valid when using TDE HSM-enabled vPDB. After executing the aforementioned steps, the Delphix workflows for the vPDB should function correctly.
